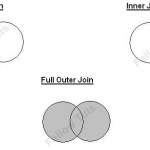
Joins are fundamental concepts in SQL and they are prefer by professionals as they are faster then sub-queries. These 3 easy MySQL examples below are a little effort to let visitors understand difference among Inner join, Left Outer join and Full outer join.
Tag » Concepts
Multiple forms on one page / controller and form validation
Sometimes it’s required to place two forms on one page in codeigniter like displaying login form and register form on same page. Although the views may be different but you can face conflict while displaying validation errors if the form actions are not separate (aren’t calling different methods in controller). Here is a workaround to validate one form at a time while placing multiple forms on one page in codeigniter.
Keep checkbox checked after form submit in Codeigniter
The set_value(‘field name’) function in codeigniter allows us to retain the value of input field in form during form submission but it’s not applicable to keep checkbox checked if it was checked while the form was submitted or during postback submit refresh. Here to keep checkbox checked after form submit in Codeigniter, the set_checkbox() function plays the role.
Working with Date in Yii 2.0
Yii is a powerful framework where a lot of things happen automagically but learning curves are more complex as compared to any other PHP MVC framework. The first part (before ‘but’ in first line) attracts beginners to learn and experience it while the later part makes them stressed. So I tried here in article Working with Date in Yii 2.0 to simplify the concept by taking ‘Date’ as point.
Embed base64 encoded images
Most modern desktop browsers such as Chrome, Mozilla, Internet Explorer supports images encoded as data url. But there are problems displaying data URLs in some mobile browsers like Android Stock Browser.
Here we are presenting that how we can embed base64 encoded images in various platforms.
Function Declaration vs Function Expression in JavaScript
There are different ways to define a function in javascript. I have seen these 2 ways to define and get confused with the differences than I googled and came across with some points which can help out to others to understand the difference between these.
Difference between Attr and Prop in jQuery
Many developers confused with the Attr and Prop keyword in jQuery. So We are describing here the difference between Attr and Prop in jQuery. The segregation of attr() and prop() should help alleviate some of the confusion between HTML attributes and DOM properties.
4 ways to empty an array in JavaScript
JavaScript arrays are commonly used by developers and making them empty is also used in practice. Here I am describing 4 ways to empty an array in JavaScript:
1. Use splice() method
2. Set length to zero
3. Using pop() method
4. Set array to new empty array
What are tags and tag cloud in WordPress?
Tags and tag cloud in WordPress are terms that quickly tell readers what a post is about and a useful way to group related posts together. A very few years ago I used to thought that tags are tricky things that are placed by bloggers to confuse people (:-D)! But soon I got familiarize with this one and so I thought to write a blog post to let readers and WordPress beginners to be familiar with tags and tag cloud.
event.preventDefault() vs. return false
event.preventDefault() vs. return false is a very important but confusing topic that which one should be used and for what. When we want to prevent other event handlers from executing after a certain event is fired, we can use one of these two techniques